Welcome to Cyber Hygiene, my weekly newsletter, where I share tips and actionable data to help everyone stay safe online.
🤖 What a Botnet Really Is
A botnet is a network of compromised devices remotely controlled by an operator, often without the owner’s knowledge.
These devices can include:
Routers
IP cameras
Printers
Servers
Cloud workloads
Smart home and office equipment
Once enrolled, devices continue to function normally while executing commands such as sending spam, launching DDoS attacks, or harvesting credentials.
Botnets are not a single malware family. They are an operational model.
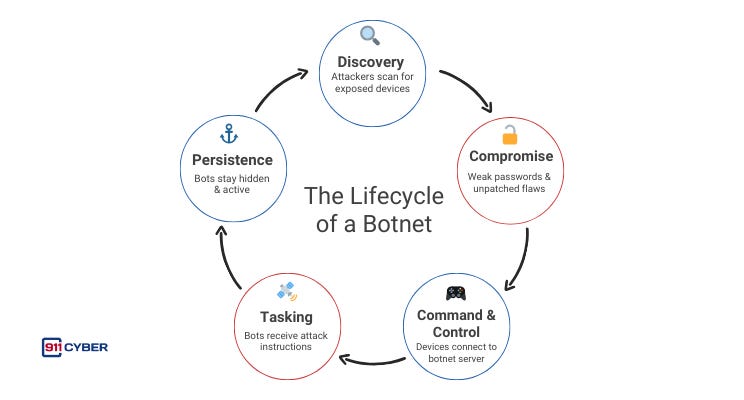
🕸️ How Does a Botnet Work
📌 Why Botnets Matter Today
Botnets are no longer just about denial-of-service attacks.
Today they enable:
Business Email Compromise at scale
Credential stuffing and account takeovers
Ransomware delivery
Ad fraud and fake engagement
AI scraping and model abuse
Infrastructure disruption
Botnets provide scale, anonymity, and resilience. That makes them fundamental to modern cybercrime economics.
Most major cybercrime operations depend on botnets at some stage.
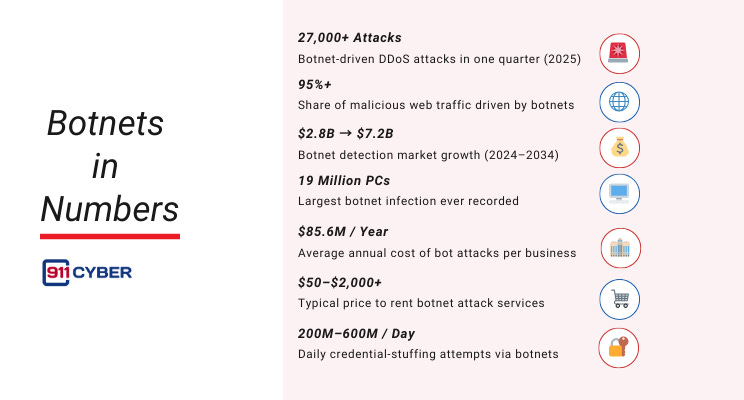
📊 Botnets in Numbers
🎯 Who’s at Risk
Individuals are often the first and easiest targets. Home routers, smart TVs, cameras, and personal devices are frequently left running with default credentials or outdated firmware. These devices are rarely monitored, always online, and trusted by default, making them ideal candidates for silent enrollment into botnets without disrupting daily use.
Small and medium-sized businesses face an even higher risk, not because they are targeted, but because they operate in the middle ground. They rely on always-on infrastructure like firewalls, printers, NAS devices, and remote access tools, yet often lack the resources or visibility to manage them continuously. Many compromises occur not through laptops, but through forgotten or unmanaged network equipment.
Certain sectors are especially exposed due to scale and complexity. Hospitality, retail, healthcare, and manufacturing environments deploy large numbers of connected devices that prioritize availability over security. When devices must stay online at all times, even minor lapses in configuration or patching can turn operational necessities into long-term botnet assets.
👀 How You’d (Not) Notice
Most botnet infections are silent.
Possible indicators include:
Internet slowdowns at unusual hours
Unexpected outbound traffic spikes
IP addresses being blocked by services
Devices running hotter than normal
Logs showing unfamiliar destinations
Many organizations only monitor inbound threats. Botnets live outbound.
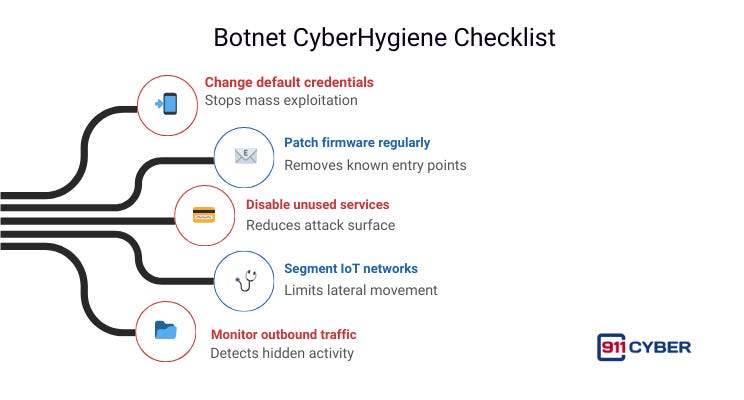
🛡️ Botnet CyberHygiene Checklist
🧠 Who Operates Botnets
Botnets are no longer controlled by a single type of attacker. They are built, rented, and repurposed across multiple ecosystems with different motivations but shared reliance on scale.
Organized cybercriminal groups and cybercrime-as-a-Service operators treat botnets like infrastructure. They lease or manage networks of compromised devices to provide services such as DDoS-for-hire, credential stuffing, spam, ad fraud, and large-scale scraping. These operations often mimic legitimate SaaS platforms with dashboards, pricing tiers, and customer support. Hacktivist collectives use botnets to amplify political messages or disrupt perceived adversaries. Visibility and impact often outweigh stealth, and campaigns can combine volunteer participation with social pressure or misinformation to rapidly scale.
State-aligned and hybrid actors use botnets in the gray zone between crime and geopolitics for disruption, intelligence collection, or strategic signaling while maintaining plausible deniability. Emerging models like DDosia show that botnets can also rely on willing participants. Users install software that turns their systems into attack nodes, incentivized by ideology, reputation, or gamification. Modern botnets can scale as effectively through social and incentive structures as through malware alone.
🧰 What Resources Are Available to Help?
📚Books
🎙️ Podcasts
Spam Botnets on Darknet Diaries, hosted by Jack Rhysider
A tale of two botnets. [Research Saturday] on CyberWire Daily with Kyle Lefton and Dave Bitner
Creepy smartwatches, botnets and Pings of Death by Sophos , presented by Kimberly Truong, Doug Aamoth and Paul Ducklin.
▶️ Videos
Coffee Break Session #110: What Is a Botnet? with Christin Cifaldil on Strategic Treasurer
🔑 Final Thoughts
Botnets are not a failure of technology. They are a failure of ownership.
As AI accelerates automation, botnets will become more adaptive, more evasive, and harder to attribute. AI will not replace botnets. It will optimize them.
The real question is not whether botnets will evolve. It’s whether we will take responsibility for the systems we connect to the internet.
In cybersecurity, the most dangerous compromises are the ones that never break anything.
Subscribe and Comment.
Copyright © 2025 @ 911Cyber All Rights Reserved.
This article was written by Marc Raphael with the support of:
Team CyberMaterial and Team 911Cyber
Follow 911Cyber on:





Excellent piece! The most important takeaway: know who’s really behind these botnets….