Cleaning Up Your Digital Closet
Forgotten accounts, old apps, and shared files quietly expand your attack surface. A 45-minute digital cleanup reduces risk, exposure, and impersonation.
Welcome to Cyber Hygiene, my weekly newsletter, where I share tips and actionable data to help everyone stay safe online.
👕 What is a “digital closet”?
Your digital closet is everything you created, signed up for, installed, shared, or stored online that you no longer actively manage.
This typically includes:
Old email addresses and usernames
Dormant social media, forum, and marketplace accounts
Apps, browser extensions, and SaaS tools you no longer use
Cloud files, shared links, and backups
Devices you no longer update or no longer own
Each one quietly expands your attack surface.
Attackers don’t need you to be careless today. They only need you to have been careless once.
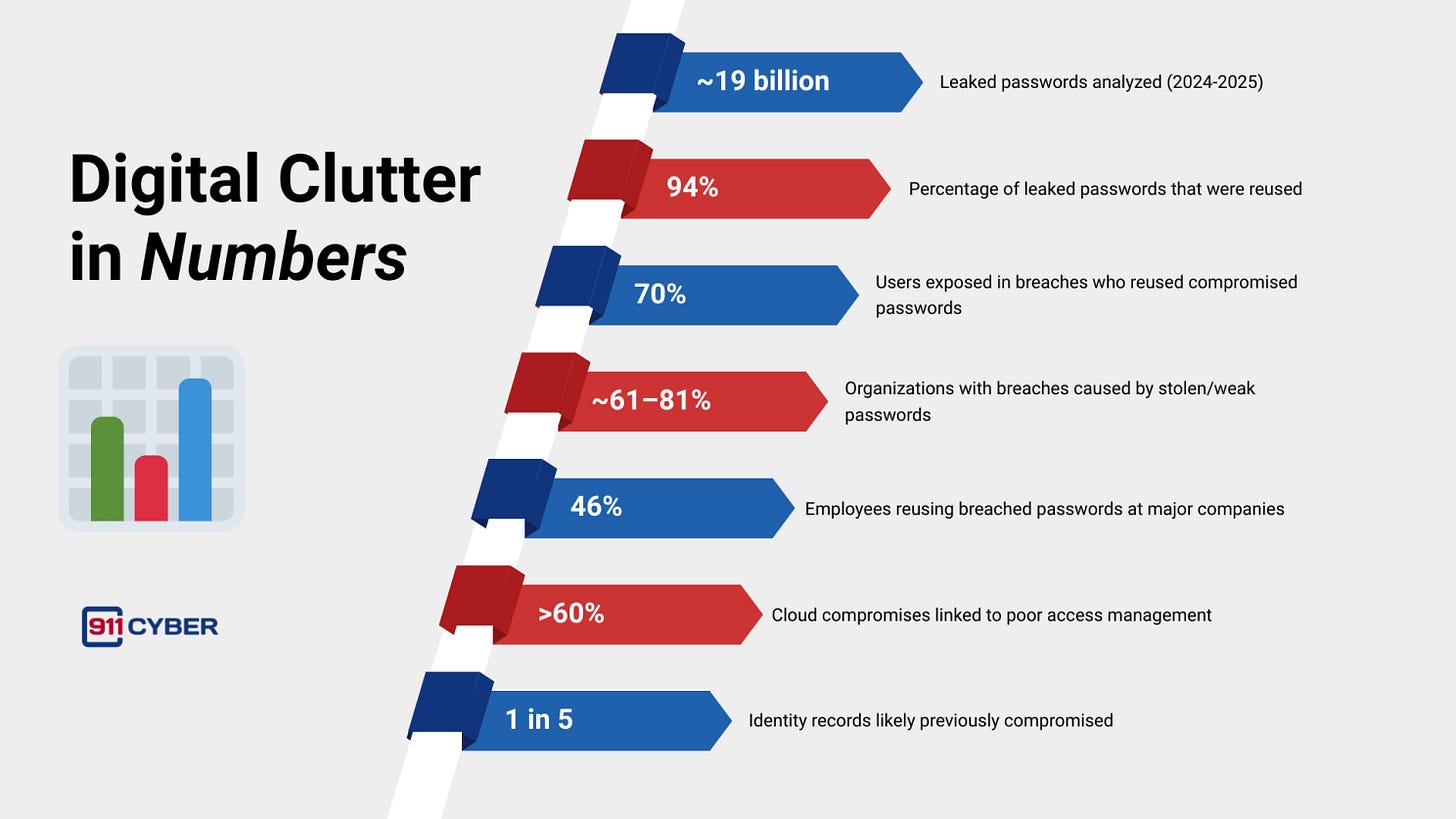
📊 Digital Clutter in Numbers
Most incidents don’t require innovation. They exploit repetition, neglect, and reuse.
The numbers consistently point to the same conclusion: weak credentials, reused passwords, and poor access management remain the dominant drivers of real-world compromises.
None of this reflects advanced attackers. It reflects predictable human behavior.
⚠️ Why Clutter Equals Risk
When forgotten digital assets are compromised, the outcomes are predictable.
Account takeover Old accounts often reuse passwords and lack modern protections like multi-factor authentication. Once compromised, they are used for fraud, spam, or as a stepping stone into other services.
Identity and reputation damage Abandoned profiles and outdated data are easy to impersonate and hard to monitor. They are frequently used in scams and social engineering campaigns.
Data exposure Old Google Docs, Dropbox folders, and shared links often remain accessible long after they stop being relevant. Many data leaks are self-inflicted and go unnoticed.
Silent compromise You won’t detect suspicious activity on an account you never check.
For scammers, credential stuffers, and social engineers, these assets are ideal: no alerts, no oversight, no resistance.
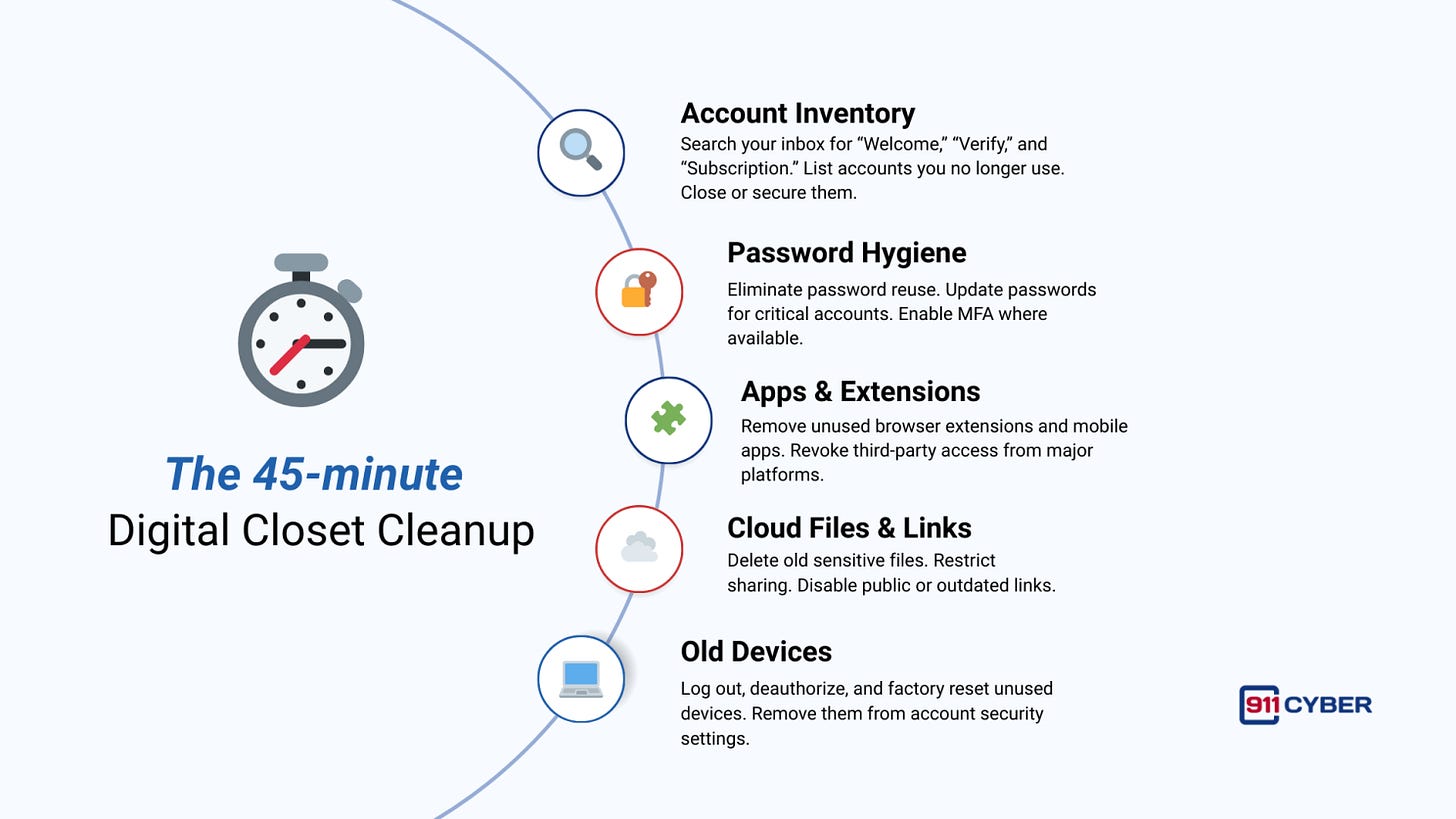
⏱️ The 45-minute Digital Closet Cleanup
🔍 Audit Your Digital Footprint
Cleaning your digital closet also means understanding what the internet already knows about you.
Start by searching for yourself. Use your full name, common variations, usernames, old email addresses, and phone numbers. Review image results as well. Outdated profiles, cached pages, data broker listings, and forgotten posts often surface quickly.
Then treat AI-powered search tools as a mirror. Ask them who you are based solely on public data. These systems summarize what already exists. If an AI can assemble a quick profile about you, so can a scammer or impersonator.
If you find information that is inaccurate, excessive, or sensitive:
Remove what you control
Lock down or delete unused profiles
Request removals from data brokers where possible
Tighten privacy settings across platforms
If you were targeted tomorrow, this is the information an attacker would start with.
🧰 What Resources Are Available to Help?
📚Books
Permanent Record by Edward Snowden
Digital Minimalism by Cal Newport
Digital Tidiness by Kara Johnson
🎙️ Podcasts
A hacker doxxes himself, and social engineering-as-a-service on Smashing Security by Graham Cluley
The Cyber Hygiene Show by Meir Niad, Rich Freiberg
Digital Hygiene by Edgar Dogourt
▶️ Videos
Essential & Simple Cyber Hygiene Tips | Tech Tangents Podcast Ep. 2 with Robert Walker and Dr. Dave Bolman
🛠️ Tools
Bitwarden - Password Manager
Mozilla Monitor – Breach Alerts
911Cyber : https://911cyber.app/report-cyber-incident/
🧹 One habit worth keeping
Digital clutter is not a technical failure. It is a maintenance failure.
If you created it, installed it, or shared it, you still own it, even if you forgot about it. Attackers do not forget. They archive.
The most effective security work is rarely visible. It does not trigger alerts or make headlines. It happens quietly, through routine cleanup and intentional ownership.
Good cyber hygiene is boring, repetitive, and invisible. And that is exactly why it works.
Subscribe and Comment.
Copyright © 2025 @ 911Cyber All Rights Reserved.
This article was written by Marc Raphael with the support of:
Team CyberMaterial and Team 911Cyber
Follow 911Cyber on: