Welcome to Cyber Hygiene, my weekly newsletter, where I share tips and actionable data to help everyone stay safe online.
📤 What Exactly Are Payment Diversion Scams?
Payment diversion scams (also called invoice fraud or funds transfer fraud) occur when cybercriminals intercept or impersonate legitimate communications about a payment and trick the victim into sending money to an account the attacker controls instead of the intended party. Unlike malware or ransomware, this attack is about deception and substitution; the money moves, but it goes to the wrong bank account.
At scale, these scams exploit:
Business email compromise (BEC)
Fake vendor invoices
Fake updated bank instructions
Email account takeovers
AI-generated impersonation
🔍 Why Payment Diversion Scams Matter to You
These scams can hit anyone who transfers funds, from individuals wiring money to settle a purchase, to businesses paying suppliers, to real estate closings and nonprofits sending payroll. Unlike “click here” attacks, payment diversion scams can:
Cause large financial losses (tens to hundreds of thousands of dollars per incident)
Compromise trust in financial workflows
Slip past traditional security controls because they rely on trusted channels
Be difficult to recover once the funds are sent
In many cases, victims only realize something is wrong when the bank tells them the funds have been cleared.
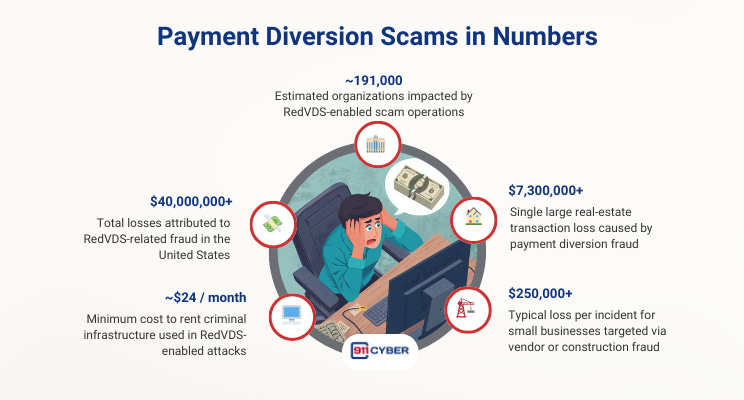
📊 Payment Diversion Scams in Numbers
👤 Who Is Behind Payment Diversion Scams?
There’s no single “villain” payment diversion scams are facilitated by a spectrum of actors:
Organized Cybercrime Groups: Professional fraud syndicates that run phishing, BEC, and diversion as a service.
Cybercrime-as-a-Service Operators: Infrastructure platforms (e.g., RedVDS) sell access to disposable servers, phishing kits, and impersonation tools.
Opportunistic Actors: Small groups or individuals who pivot into diversion when automation makes it easy and profitable.
Insider Threats: Employees, contractors, or vendors with legitimate access to payment workflows who manipulate instructions or share sensitive information, intentionally or under coercion.
Their common goal: trick trusting parties during critical payment moments.
🔄 How Do Payment Diversion Scams Happen?
🤖 What Are the Latest Trends
Payment diversion tactics are evolving for three reasons:
1. AI-Generated Impersonation
Attackers can now:
Clone voices
Generate realistic video of executives
Write highly personalized emails This makes impersonation indistinguishable from legitimate contacts.
2. Automation at Scale
Crime services sell turnkey tools:
Phishing templates
Scripts for invoice manipulation
Disposable infrastructure These lower the bar for attackers.
3. Blended Social Engineering
Attackers combine AI outputs with well-timed social engineering:
AI drafts the perfect pretext
Human attackers adjust for context This results in far higher success rates than dumb spam.
The bottom line: AI turns volume scams into precision attacks.
🛡 How to Protect Against Payment Diversion Scams
🧰 What Resources Are Available to Help?
📚Books
🎙️ Podcasts
Episode 27: Payment Diversion Fraud in the Legal Sector by National Crime Agency
Fraud Risks in Real-Time Payments | Connecting the Dots in Payments on podcast What the Fraud? With Thomas Taraniuk and Arthur Bedel
Payment Diversion Fraud - Gemma’s Story by City of London Police
▶️ Videos
Unmasking Money Mules: “The Evolution of a Scammer” (Financial Crime Podcast Episode 5) with Brett Johnson
🔑 Final Thoughts
Payment diversion scams aren’t about technology failing. They’re about trust being exploited at the right moment.
AI makes the deception sharper, faster, and harder to detect. But the real weakness isn’t the hacker. It’s the process we leave exposed.
Every familiar email. Every routine invoice. Every “small” change to payment details is a potential trigger.
Cybersecurity isn’t just about stopping breaches. It’s about designing workflows that don’t let a single message move your money.
So ask yourself: are you protecting your systems, or just hoping no one notices when trust gets hijacked?
Subscribe and Comment.
Copyright © 2025 @ 911Cyber All Rights Reserved.
This article was written by Marc Raphael with the support of:
Team CyberMaterial and Team 911Cyber
Follow 911Cyber on: