Cybersecurity is at an inflection point. Not because attackers suddenly got smarter, but because defenders are reaching the limits of what human-centered security can sustain.
Alert fatigue, talent shortages, accelerating attack speeds, and expanding attack surfaces are colliding at once. The result is a simple truth the industry has been slow to admit: humans alone can no longer run cyber defense at machine speed.
This is where autonomous cyber enters the conversation. Not as a buzzword, but as an operational necessity.
What Autonomous Cyber Actually Means
Autonomous cyber is not about replacing humans with AI. It is about shifting decision-making and action to machines where speed, scale, and consistency matter most, while keeping humans firmly in charge of intent, policy, and accountability.
In practice, this means systems that can:
Detect threats continuously
Make risk-based decisions in real time
Take corrective action within defined guardrails
Learn and adapt from outcomes
Think of it as the shift from:
“alert → analyst → decision → action”
to
“signal → decision → action (with humans supervising)”
Humans don’t disappear. They move upstream, from reacting to incidents to designing how systems should behave under risk.
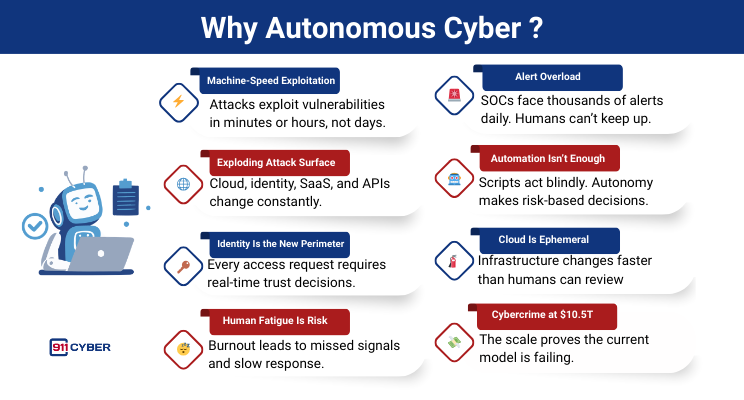
Why Is Autonomous Cyber Needed?
Here are some of the leading reasons why autonomous cybersecurity is moving beyond something nice-to-have to a must-have.
1. Automation Isn’t Enough Anymore
People very often confuse automation with autonomy. While automation helps accelerate certain processes by removing direct human executions, it still waits for humans to decide when and how to act.
That bottleneck kills speed.
Autonomous cyber removes the decision lag by:
Making risk-based decisions
Acting within predefined guardrails
Escalating only true exceptions
This is the difference between scripts and systems.
Automation, or a “script,” is a blind, static IF/THEN rule that acts without context, like isolating a device for any alert, potentially disrupting critical operations.
Autonomy, or a “system,” makes continuous, risk-based decisions, allowing for dynamic actions like revoking a specific cloud token to mitigate risk without causing a full business outage.
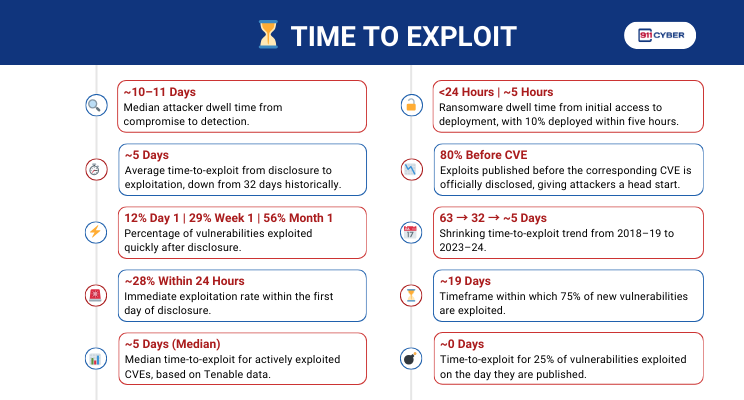
2. Time To Exploit
Attacks Move at Machine Speed. Humans Don’t.
Modern attacks execute credential abuse, lateral movement, data exfiltration, cloud resource hijacking in seconds.
Even the best SOC response measured in minutes is already too slow.
Autonomous systems can detect, decide, and act in real time, without waiting for human approval.
ecurity teams don’t fail because they’re bad. They fail because they’re flooded. Their SOCs receive millions of events per day, thousands of alerts per analyst. Most alerts are low value or false positives
Autonomy is needed to suppress noise, decide what matters and act on routine threats automatically. Without it, defenders burn out and real threats slip through.
3.Attack Surface Too Complex for Manual Control
Security now spans:
Cloud and on-prem
SaaS and APIs
Identities and devices
AI systems and third-party risk
No human or team can continuously reason across all of this in real time. Autonomous cyber provides continuous, cross-domain decision-making humans simply can’t sustain.
4.Identity and Cloud Demand Continuous Decisions
Identity and cloud environments are dynamic and probabilistic by nature. Every access request, API call, or workload change depends on context such as behavior, device posture, location, and system state. Risk-based authentication and dynamic access controls already rely on machines because there is no fixed “safe” state. Cloud infrastructure is ephemeral, with assets and permissions changing constantly.
Periodic human review cannot keep up with this pace. By the time a manual check happens, the risk has already shifted. These environments require continuous evaluation and real-time decisions to grant, restrict, or revoke access. In identity and cloud security, autonomy is not optional; it is foundational.
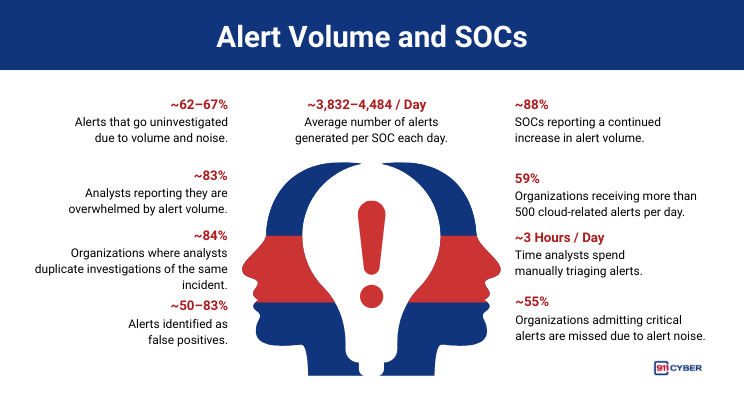
5.Alert Volume Has Broken the SOC
Most security teams don’t fail because they’re bad. They fail because they’re flooded. Their SOCs receive millions of events per day, thousands of alerts per analyst. Most alerts are low value or false positives
Autonomy is needed to suppress noise, decide what matters and act on routine threats automatically. Without it, defenders burn out and real threats slip through.
6.Human Fatigue Is Now a Security Risk
Human Fatigue Is Now a Security Risk. Burnout isn’t a staffing problem. It’s a risk factor. Overworked teams miss signals,delay response, make inconsistent decisions.
Autonomous cyber absorbs the repetitive, high-volume work so humans can focus on strategy, oversight, accountability.
7.High-Risk Industries Already Made the Shift
Aviation, finance, and industrial control systems rely on autonomy because:
Speed matters
Failure is costly
Human reaction time is insufficient
Cybersecurity is now just as critical and just as time-sensitive.
A key takeaway from these shifts is that these industries established robust fail-safes and regulatory oversight alongside autonomy, a crucial next discussion for cyber.
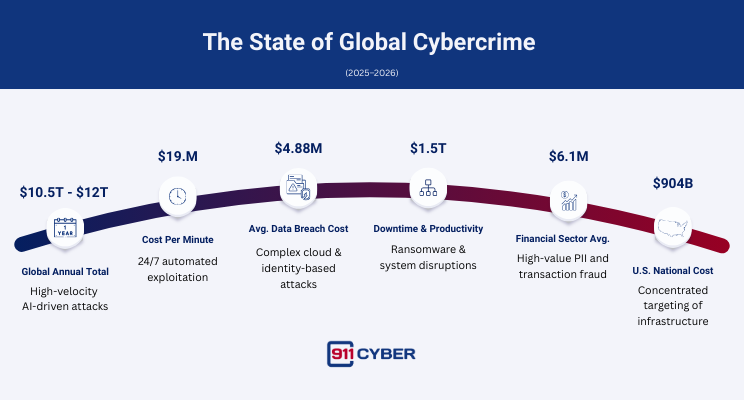
8.The $10.5 Trillion Cost of Cybercrime
This staggering economic figure serves as the ultimate justification for autonomous cyber.
It is evidence that human-centered security has reached its operational limits and is unable to contain the growth of machine-speed threats.
The current defense model is failing at a colossal scale, making a shift to autonomous systems an urgent financial necessity to reverse this trend.
Final Thoughts
The transition to autonomous cyber is not a matter of ‘if,’ but a necessity for survival. The current model (where human speed confronts machine speed) has failed, as evidenced by the unmanageable alert volume, expanding attack surface, and the staggering $10.5 trillion cost of cybercrime.
By shifting real-time decision-making and action to autonomous systems, we can finally move human defenders upstream to focus on strategy, policy design, and accountability.
Autonomous cyber is perhaps the only operational path forward to secure the digital world at the speed and scale the modern threat landscape demands.
Sources:
https://www.ibm.com/reports/data-breach
https://cloud.google.com/blog/topics/threat-intelligence/m-trends-2025
https://www.google.com/search?q=https://www.sophos.com/en-us/content/active-adversary-report
https://www.first.org/blog/20260211-vulnerability-forecast-2026
https://deepstrike.io/blog/vulnerability-statistics-2025
https://cybersecurityventures.com/cybercrime-damage-costs-10-trillion-by-2025/
https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2026.pdf
https://www.bdemerson.com/article/complete-cybercrime-statistics
https://deepstrike.io/blog/cybercrime-statistics-2025
Subscribe and Comment.
Copyright © 2026 @ 911Cyber All Rights Reserved.
This article was written by Marc Raphael with the support of:
Team CyberMaterial and Team 911Cyber
Follow 911Cyber on: https://linktr.ee/911cyber