The State of Autonomous Cyber: 2026
Cybersecurity is no longer a human-speed discipline.
As we move through 2026, the industry has crossed a structural inflection point. We are transitioning from AI-assisted security to AI-native security operations. The $10.5 trillion annual global cost of cybercrime is not just a statistic. It is economic proof that human-centric defense models cannot scale to machine-speed threats.The question is no longer whether autonomy will emerge in cybersecurity. The question is how far we have actually progressed.
1. If autonomy is inevitable, how far are we actually?
We are currently in the Agentic Era. While 2024 was about chatbots and copilots, 2026 is defined by Autonomous Agents. These are software entities that can reason, remember, and execute multi-step workflows without a human prompting every move.
Adoption:
77% of global organizations have now integrated AI into their security stacks.
The Shift:
We have moved from static logic to Dynamic Exposure Management. Systems now identify a new vulnerability and automatically simulate attack paths to decide whether to patch, shield, or ignore it based on business context.
2. Where is autonomy already real and operational?
Autonomy has matured in high-volume, low-context domains where speed is the only metric that matters.
Tier 1 SOC Operations
The first line of defense is now largely autonomous. AI agents handle 90% of triage, investigation, and incident classification. This reduces Mean Time to Contain (MTTC) by over 100 days compared to manual SOCs.
Phishing and Identity
AI-powered email security now catches 99% of phishing attempts, adapting in real time to deepfake voice and video clones.
Cloud and Micro-segmentation
In ephemeral cloud environments, autonomous systems handle the quarantine of compromised containers in milliseconds. This is far faster than a human could even log into a console.
3. Where It Breaks Down: The Core Challenges
Autonomy is not a silver bullet. It breaks down in three critical areas.
The Hallucination of Intent
Machines struggle to distinguish between a malicious admin and a stressed admin performing an emergency workaround. Contextual nuances still lead to over-blocking, which can halt business operations.
Adversarial AI
Attackers are using the same autonomous agents to rewrite malware code on the fly. This creates an AI arms race where defensive models must be retrained daily to stay relevant.
Supply Chain Opacity
Autonomy relies on data. When a third party vendor’s autonomous agent interacts with yours, a trust gap emerges. One compromised agent can trigger a cascade of automated failures across an entire ecosystem.
4. The Autonomous Cyber Maturity Model
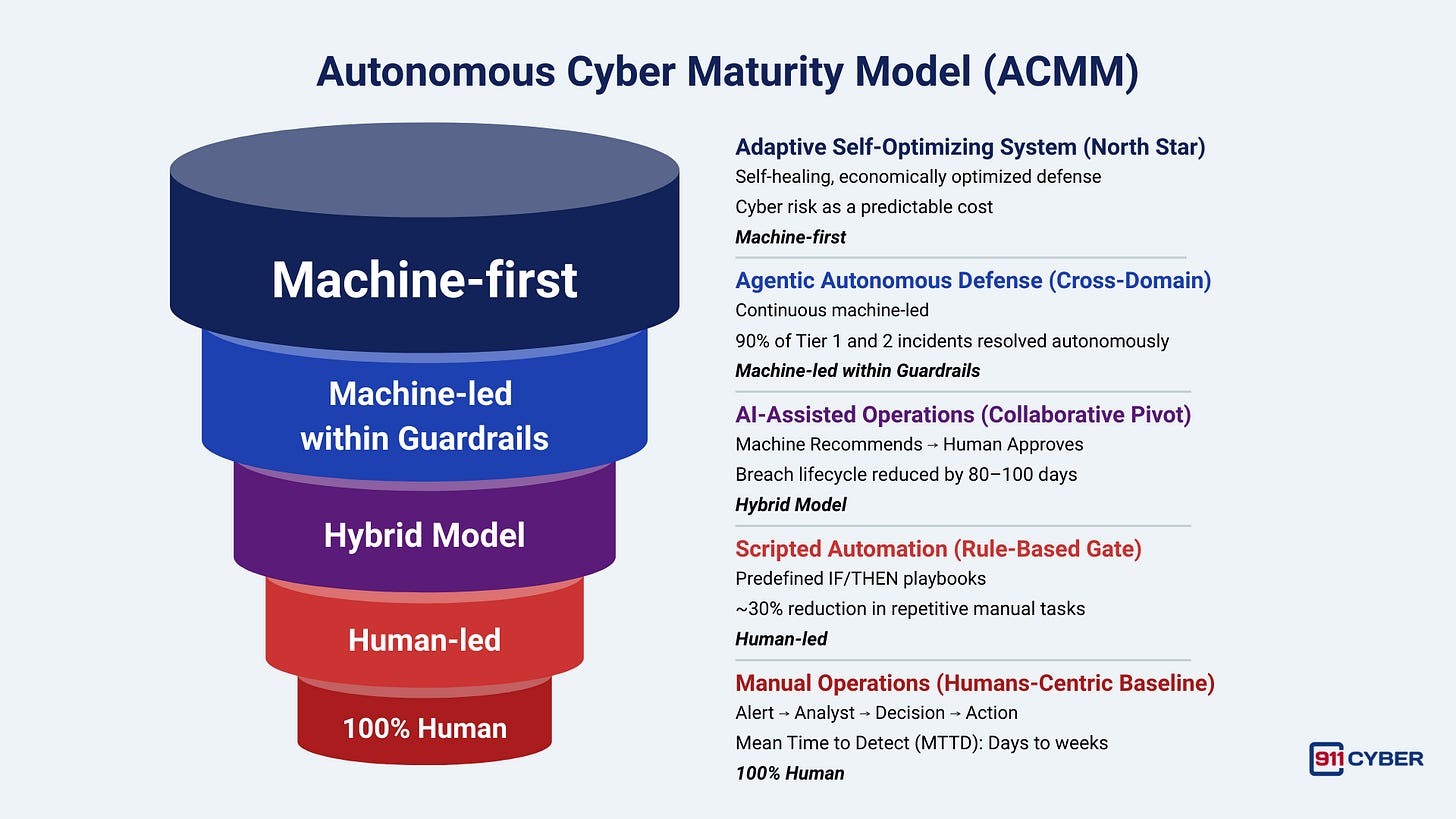
To move beyond the hype, we must utilize the Autonomous Cyber Maturity Model.
It begins at Level 1 (Manual Operations), a human-centric baseline where people perform all analysis and decision-making while machines serve as simple alert-generators. This stage is defined by high burnout, tribal knowledge, and detection times measured in days or weeks.
Transitioning to Level 2 (Scripted Automation) introduces rigid SOAR playbooks and “if-then” logic. While this reduces repetitive tasks by 30%, the system remains inflexible, and machines cannot “think” beyond their pre-written scripts.
Level 3 (AI-Assisted Operations) is the 2026 industry standard, representing a collaborative pivot where machine learning handles risk-scoring and behavioral analytics. In this hybrid model, machines recommend actions while humans provide final approval, effectively reducing the breach lifecycle by up to 100 days.
The true breakthrough occurs at Level 4 (Agentic Autonomous Defense), where cross-domain agents treat identity, cloud, and network as a unified fabric. Here, systems make business-aware decisions and execute remediations autonomously within guardrails, resolving 90% of mid-tier incidents without human interference.
The “North Star” is Level 5 (Adaptive Self-Optimizing System). At this pinnacle, the environment is self-healing and performs complex economic trade-offs, such as weighing the cost of downtime against cloud scaling expenses. Humans transition from operators to policy authors and safety engineers, while the system dynamically tunes risk tolerances to align with revenue goals. This transforms cybersecurity from an unpredictable threat into a predictable, manageable line item on the balance sheet.
5. Final Thoughts
Autonomous cyber is neither fully realized nor speculative fiction. It is unevenly distributed.
Tier 1 triage, phishing defense, cloud containment, and exposure modeling are already machine-led in advanced environments. Strategic decision-making, cross-organization governance, and economic optimization remain human-dominated.
The industry is currently clustered between Level 3 and early Level 4 maturity.
The defining question for the next five years is not whether autonomy will expand. It will.
The real questions are:
Can governance mature at the same pace as capability?
Can organizations redefine roles before displacement creates instability?
Can we prevent autonomous defense from amplifying systemic risk?
Autonomous cyber is not about replacing humans. It is about reallocating human cognition to where it creates the most leverage: intent, accountability, policy design, and strategic risk modeling. The future of cybersecurity will not be human versus machine. It will be defined by how effectively humans design machines that defend at machine speed.
6. Self-Assessment Quiz
To help you assess where your organization or your knowledge stands in this transition, I have generated a Self-Assessment Quiz based on the Autonomous Cyber Maturity Model (ACMM).
This quiz will test your understanding of the different levels of autonomy, the core challenges of machine-led defense, and the metrics used to measure success in 2026.
Sources:
IBM Cost of a Data Breach Report 2025: https://www.ibm.com/reports/data-breach
World Economic Forum Global Cybersecurity Outlook 2026: https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2026.pdf
Sophos Active Adversary Report 2025: https://www.sophos.com/en-us/content/active-adversary-report
Mandiant M-Trends 2025: https://cloud.google.com/blog/topics/threat-intelligence/m-trends-2025
CISA / FIRST Vulnerability Forecast 2026: https://www.first.org/blog/20260211-vulnerability-forecast-2026
Cybersecurity Ventures 2025 Report: https://cybersecurityventures.com/cybercrime-damage-costs-10-trillion-by-2025/
Bluefin IBM 2025 Findings:https://www.bluefin.com/bluefin-news/ibms-2025-data-breach-report-key-findings-and-the-years-biggest-attacks/
Subscribe and Comment.
Copyright © 2026 @ 911Cyber All Rights Reserved.
This article was written by Marc Raphael with the support of:
Team CyberMaterial and Team 911Cyber
Follow 911Cyber on: https://linktr.ee/911cyber