What does AI know about you?
This edition of CyberHygiene examines how everyday AI collects and connects personal data, highlighting its impact on users without sensationalism.
Welcome to Cyber Hygiene, my weekly newsletter, where I share tips and actionable data to help everyone stay safe online.
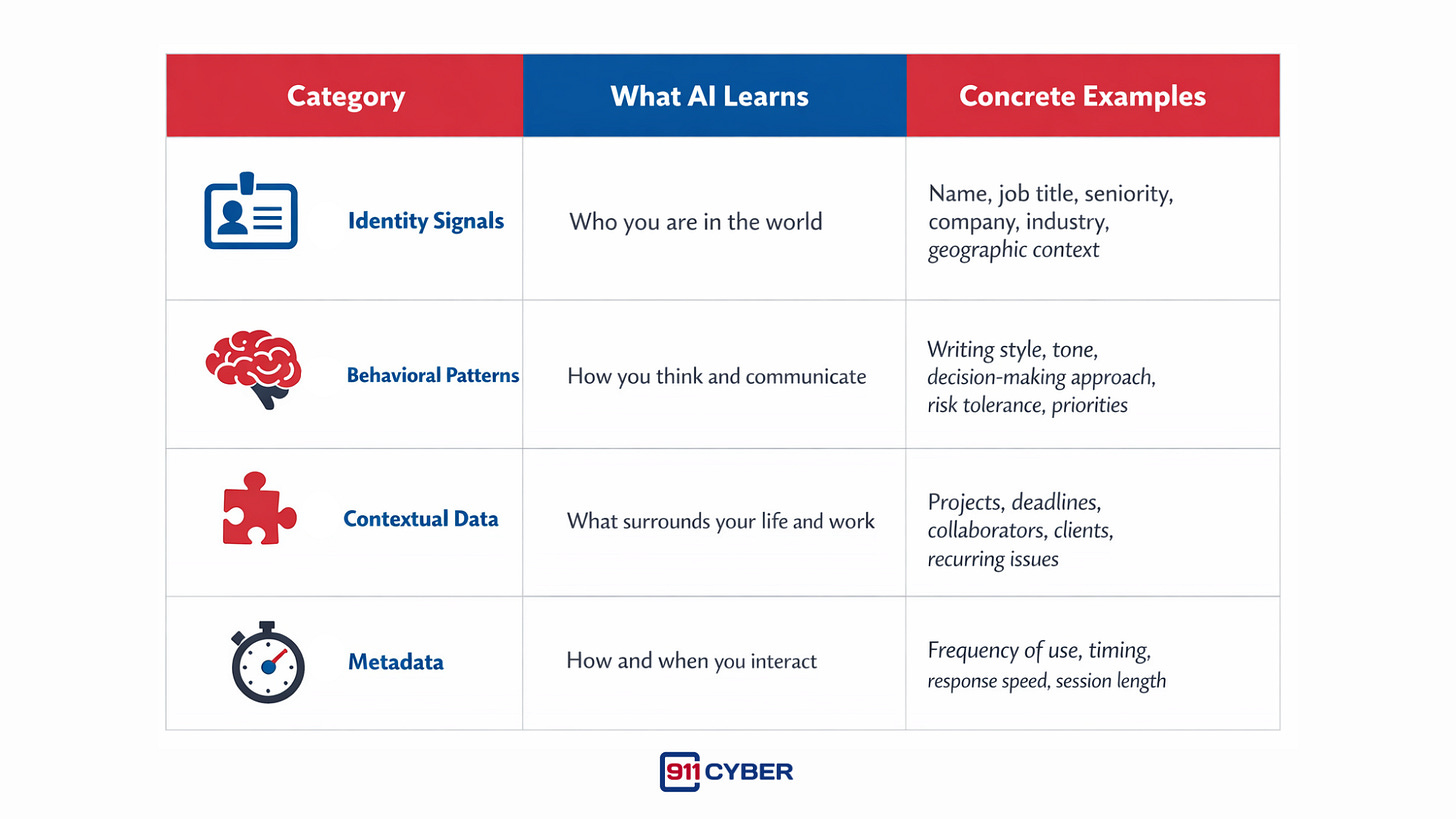
🤖 What AI Actually Learns About You
AI systems do not need to be told who you are to learn about you. They infer.
Over time, routine interactions reveal several categories of information:
The key point is simple but often overlooked:
AI does not need explicit personal data to generate personal insight.
Patterns are enough.
⚠️Why Aggregation Is the Real Risk
The primary risk introduced by AI is not surveillance.
It is aggregation.
Historically, personal data was fragmented across many services. One platform held emails, another documents, another social interactions, another search history.
AI increasingly operates across these layers.
When fewer systems hold richer, interconnected context, several things change:
Breaches become more damaging because the data is more complete
Misuse becomes more precise because context already exists
Internal access carries greater consequences
Errors or misinterpretations propagate faster
Old data remains relevant longer than intended
This is not an accusation against AI vendors.
It is a description of structural risk created by consolidation.
Good intentions do not eliminate architectural exposure.
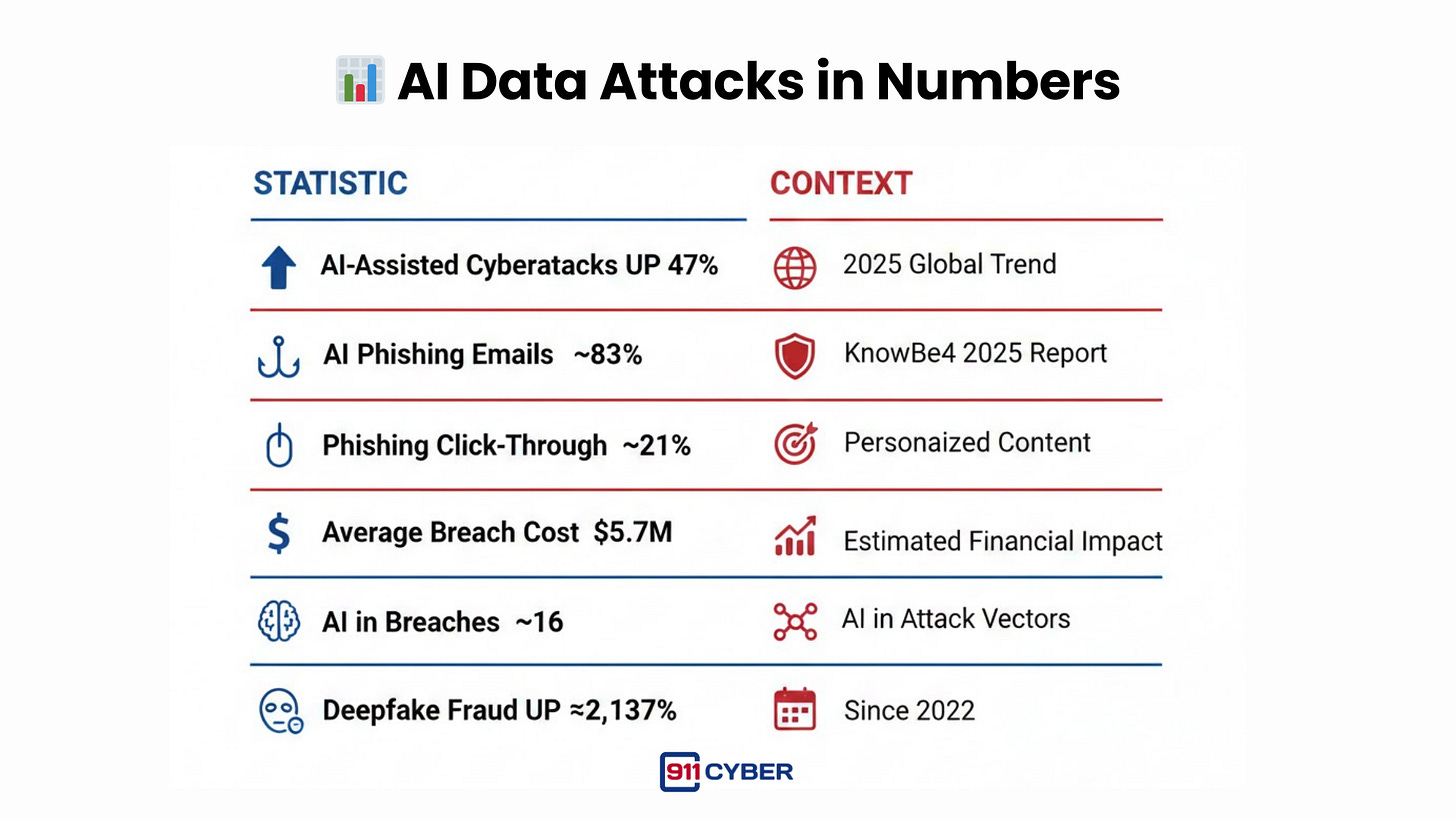
📊 AI Data Attacks in Numbers
🕶️ AI Glasses as a Concrete Example
AI glasses attract attention because they are visible.
A camera.
A microphone.
A device that looks back at the world.
They make people uneasy because recording is obvious.
But the deeper issue is not being recorded.
It is being recognized and contextualized.
AI glasses combine:
Vision with cloud-based profiles
Real-time identification with existing data
Contextual overlays with historical information
Ephemeral moments with persistent records
They do not create a new privacy problem.
They expose how mature the data ecosystem already is.
AI glasses simply make visible what is otherwise abstract:
how quickly identity, context, and history can be assembled when enough data already exists.
🎯 How This Data Can Be Used Against People
When personal context is aggregated, abuse does not require advanced techniques.
Plausible, real-world outcomes include:
Hyper-personalized phishing that mirrors tone, timing, and real projects
Convincing impersonation using accurate language and references
Reputation manipulation built from partial truths and contextual details
Social engineering at scale that exploits trust and familiarity
These attacks succeed not because they are technically sophisticated, but because they feel authentic.
Context lowers friction. Familiarity lowers suspicion.
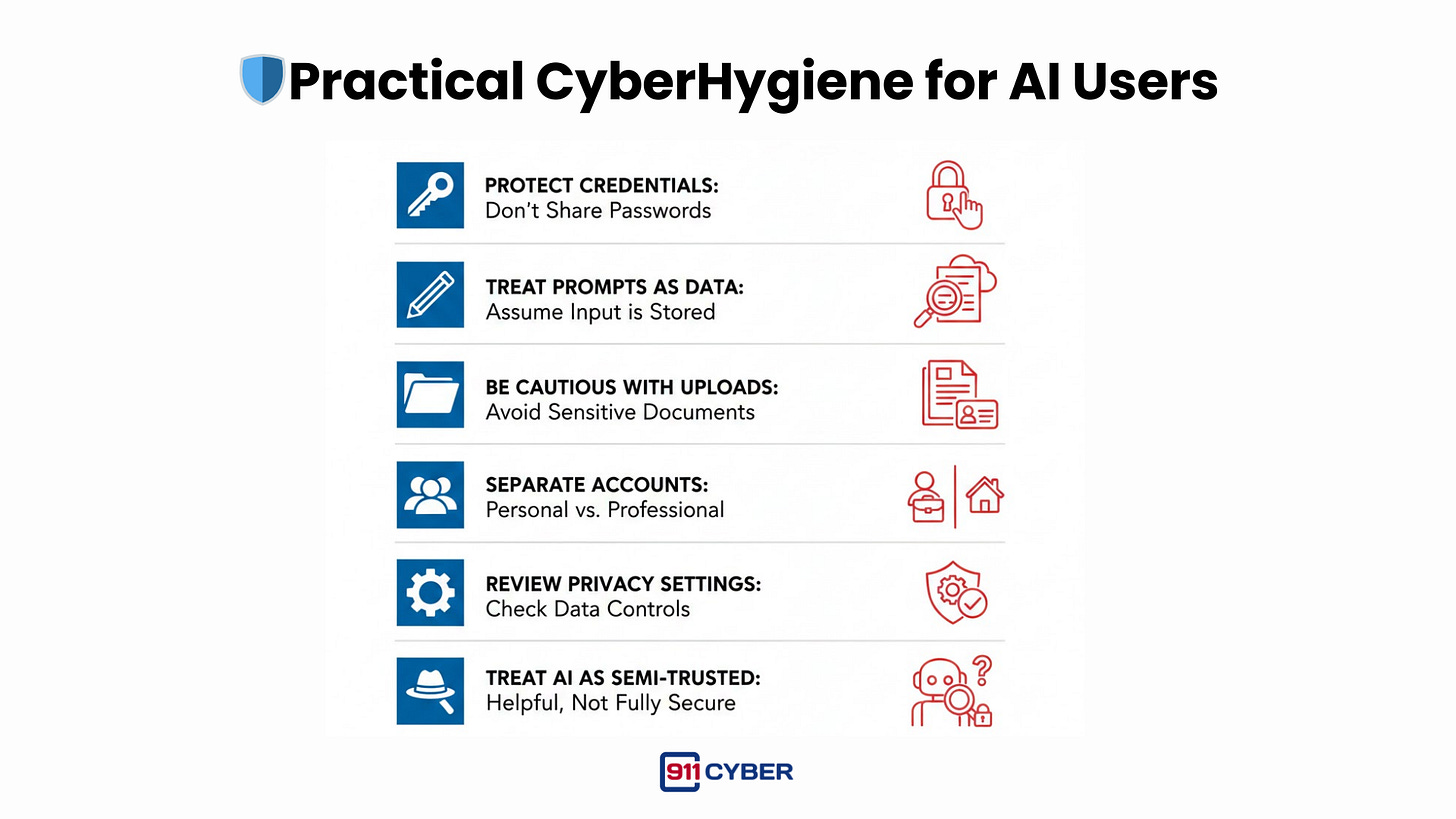
🛡️Practical Tips for AI Users
You do not need to stop using AI.
You need to use it intentionally.
Practical CyberHygiene includes:
🧰 What Resources Are Available to Help?
📚Books
AI Data Privacy and Protection: The Complete Guide to Ethical AI, Data Privacy, and Security by Justin Ryan, Mario Lazo
Beyond the Algorithm: AI, Security, Privacy, and Ethics by Omar Santos, Petar Radanliev
Generative AI for Cybersecurity and Privacy by Youssef Baddi, Yassine Maleh, Izzat Alsmadi, Mohamed Lahby.
🎙️ Podcasts
Smashing Security – Graham Cluley & Carole Theriault
The Cyber Hygiene Show – Meir Niad & Rich Freiberg
Digital Hygiene – Edgar Dogourt
▶️ Videos
Cybersecurity in the Age of AI & Social Engineering | Tech Tangents Podcast Ep. 2 with Robert Walker & Dr. Dave Bolman
🔑 Final Thoughts
AI is not inherently hostile to users.
But it changes the economics of personal data.
CyberHygiene in the age of AI is not about avoiding tools or rejecting progress. It is about understanding what accumulates, where it lives, and how long it lasts.
The most important question is no longer whether AI is safe.
It is:
What does AI already know about you, and who else might want that information?
Awareness, boundaries, and deliberate use remain the most effective forms of protection.
Subscribe and Comment.
Copyright © 2025 @ 911Cyber All Rights Reserved.
This article was written by Marc Raphael with the support of:
Team CyberMaterial and Team 911Cyber
Follow 911Cyber on: